Acknowledgments
Introduction
Chapter 1: Bash Basics
Chapter 2: Flow Control and Text Processing
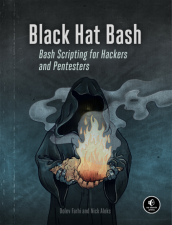
Chapter 3: Setting Up a Hacking Lab
Chapter 4: Reconnaissance
Chapter 5: Vulnerability Scanning and Fuzzing
Chapter 6: Gaining a Web Shell
Chapter 7: Reverse Shells
Chapter 8: Local Information Gathering
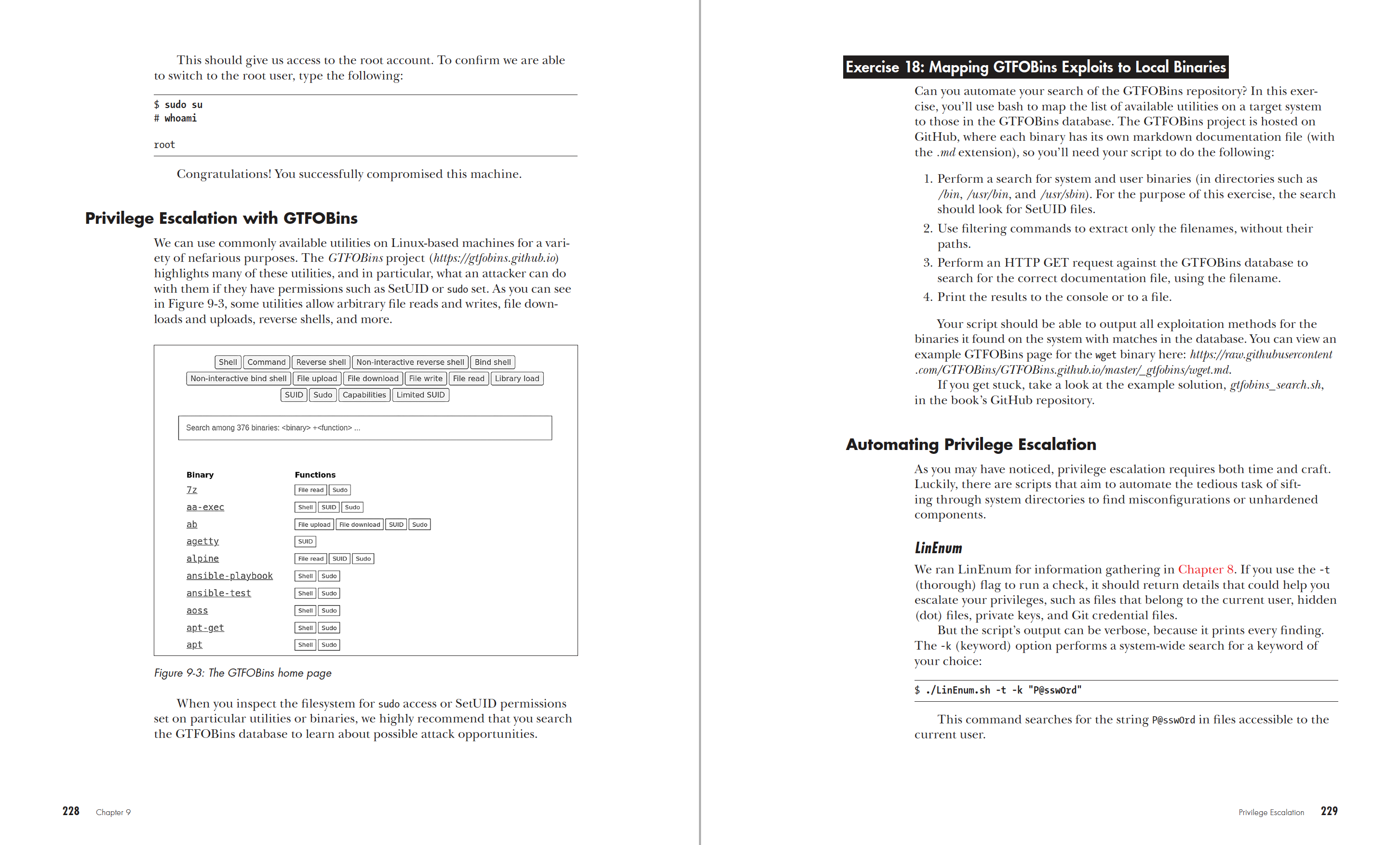
Chapter 9: Privilege Escalation
Chapter 10: Persistence
Chapter 11: Lateral Movement and Network Probing
Chapter 12: Defensive Evasion and Exfiltration
Index
The chapters in red are included in this Early Access PDF.